With its unprecedented ability to process information at extraordinary speed and complexity, quantum technology has the potential to redefine how we safeguard our most sensitive data.
Today, most digital security systems that protect transactions, personal information, and communications rely on a simple principle: creating mechanisms that make decryption without authorization extremely difficult.
Encryption algorithms such as RSA and ECC form the backbone of this model. In essence, these systems work because encrypting data is straightforward, but decrypting it without the proper key is practically impossible.
In RSA, for example, decryption would require factoring enormous numbers—a computational task far beyond the reach of current machines. ECC (Elliptic Curve Cryptography) achieves comparable security through a different mathematical foundation, providing strong protection with smaller and more efficient keys.
This algorithmic approach has been remarkably effective for decades, serving as the foundation of modern digital security. Yet, the rapid advance of quantum computing represents a fundamental shift in how information can be processed.
Why Encryption Needs a Quantum Rethink

Unlike conventional computers that use binary bits—values of 0 or 1—quantum computers operate with qubits, which can exist in multiple states simultaneously through the principles of superposition and entanglement.
This quantum behavior enables certain calculations to be performed exponentially faster than classical systems ever could. But that same power also threatens to undermine traditional encryption, since the mathematical problems on which RSA or ECC rely could be solved far more efficiently in a quantum framework.
In this light, quantum cryptography is not a reactive defense, but a natural evolution of cybersecurity. Instead of depending on computational difficulty, it draws on the unbreakable laws of physics to protect information. More than a technological upgrade, it represents a transformation in how we define digital trust—offering a foundation built for a future where information security must keep pace with quantum intelligence itself.
What is Quantum Cryptography and How Does it Work?

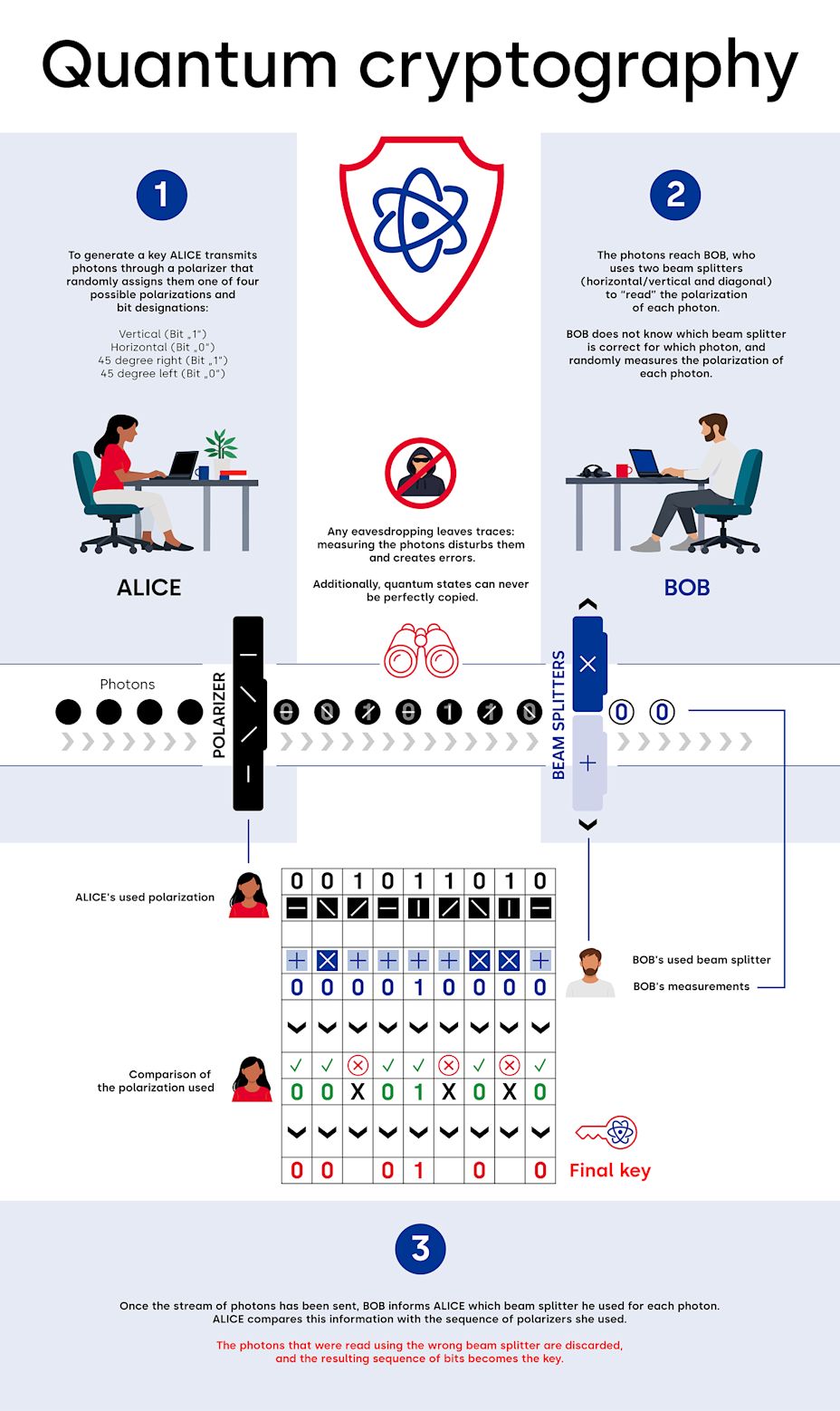
Quantum cryptography is a collection of techniques that apply the principles of quantum mechanics—a branch of physics that studies subatomic particles—to guarantee the security of communications. Its most widely known application is Quantum Key Distribution (QKD), which uses Heisenberg’s uncertainty principle and the phenomenon of quantum entanglement to ensure that any attempt at interception can be immediately detected.
In QKD, information is transmitted through quantum particles whose physical properties change when observed. This means that any interception effort alters the system, leaving a detectable trace. If interference is detected, the keys are discarded and the process is restarted, ensuring that only legitimate parties share the information securely.
Rather than replacing traditional encryption, QKD reinforces it. Once a key is securely exchanged through quantum means, it can be used within conventional encryption systems to protect data transmission. QKD networks can also integrate with existing fiber-optic infrastructures, and satellite-based systems are under development to extend their global reach. These applications are not meant to immediately replace current methods, but to add an extra layer of protection for high-value information with long-term sensitivity.
Beyond Key Distribution: Quantum Teleportation

Quantum cryptography builds on fundamental concepts of quantum physics that are also inspiring other emerging technologies. One of the most fascinating examples is quantum teleportation—a process that enables the quantum state of one particle to be transferred to another, distant particle, without physically moving the original.
Although it does not involve transmitting data in the traditional sense, quantum teleportation demonstrates how information can be securely and precisely communicated through quantum entanglement. This principle reinforces a core idea of quantum security: protection does not rely on concealing information, but on ensuring that any attempt at interference leaves an unmistakable trace.
From Power Grids to Military Bases

Quantum cryptography is beginning to transform how critical information is secured, particularly in sectors where communication must be absolutely tamper-proof. Governments and operators of strategic infrastructure—such as power grids, transport networks, and telecommunications control centers—are exploring Quantum Key Distribution (QKD) to ensure that data remains protected even in a future dominated by quantum computing.
Across the world, pilot projects have tested QKD in secure communication links between embassies, military installations, and other state institutions, demonstrating its potential to dramatically reduce the risk of intrusion or espionage.
Safer Financial Transactions

The financial industry is also advancing rapidly in this field. Banks such as Banco Sabadell and Intesa Sanpaolo are already applying quantum-inspired methods to enhance risk modeling and fraud detection through machine learning. In the United Kingdom—where banking fraud reached $1.6 billion in 2024—quantum technologies are becoming a national priority, with $162 million in new investments aimed at combating cybercrime, fraud, and money laundering.
Risk management remains one of the most critical pillars of the financial system. Turkish bank Yapı Kredi, for instance, developed a model to identify vulnerabilities within its network of small and medium-sized enterprises, preventing a potential chain reaction of financial distress. An analysis that once required years was completed in just seven seconds.
HSBC, meanwhile, has explored quantum-resistant security solutions to safeguard digital assets such as tokenized gold. In pilot initiatives, the bank has employed post-quantum cryptography (PQC) to maintain interoperability between token systems and has integrated quantum random number generators (QRNG)—notably Quantinuum’s “Quantum Origin” technology—to strengthen key generation and enhance overall cryptographic resilience.
Comprehensive Transformation of the Health Industry

Hospitals and research institutions handle vast amounts of highly sensitive information, from patient records to clinical trial results. Quantum Key Distribution (QKD) offers a way to ensure that this data is transmitted securely between facilities, protecting privacy and minimizing the risk of breaches or manipulation.
In India, companies such as QNu Labs are developing quantum cryptography solutions specifically designed to safeguard sensitive health and research data. Meanwhile, in Spain, Vithas Hospitals conducted a real-world pilot project to test the feasibility of securing sensitive communications with QKD, using LuxQuanta equipment and a Quantum-Safe solution developed by QoolNet-UPM. The encryption keys generated through QKD were integrated with next-generation firewalls, creating an end-to-end encrypted communication channel. The project was presented at the 2025 Mobile World Congress (MWC), marking an important milestone in the application of quantum security to healthcare.
Fortifying Smart Cities and the IoT

Connected devices—urban sensors, traffic lights, surveillance cameras, smart meters, and public transport systems—represent one of the most vulnerable frontiers in cybersecurity. Their limited computational power, constant connectivity, and large-scale deployment make them particularly exposed to attacks.
To address this, smart cities are beginning to adopt hybrid security frameworks that combine QKD with conventional IoT (Internet of Things) infrastructures. This hybrid approach enables quantum-resistant protection without requiring costly or complex quantum hardware on each device. By integrating QKD with lightweight communication protocols such as MQTT (Message Queuing Telemetry Transport) and CoAP (Constrained Application Protocol), secure encryption keys can be distributed to IoT devices efficiently, even in constrained environments.
Since 2024, more than 30 cities worldwide have launched pilot QKD networks, a number expected to double by the end of 2025. Countries including China, South Korea, and the United States are accelerating investments in quantum-resilient infrastructure, focusing particularly on critical urban systems—energy, transport, and communication—where security breaches could have widespread impacts.
The Big Hurdle: Implementation Costs
Quantum cryptography holds extraordinary promise, but its adoption faces practical and financial challenges. The technology requires specialized infrastructure and substantial investment. Establishing a single QKD link can cost between $50,000 and $100,000, while deploying a full-scale network can easily exceed one million dollars. As of 2023, fewer than 10% of telecommunications operators reported being ready to implement quantum security on a large scale.
Distance and scalability also remain significant technical hurdles. Current systems often rely on hybrid networks or quantum satellites to extend their range. The Jinan-1 microsatellite, operational since 2025, has demonstrated real-time quantum key distribution between multiple ground stations, achieving distances of up to 12,900 kilometers between China and South Africa—a major step toward global quantum-secure communication.
Hybridization with Classical Encryption: the Key to Progress

Quantum cryptography is not intended to replace traditional encryption, but to complement and reinforce it. Integrating QKD into existing digital infrastructures allows organizations to prepare for future threats without disrupting present-day operations. This hybrid approach enables gradual, strategic adoption while maintaining continuity and reliability.
The global market for quantum cryptography reached $717 million in 2024 and is expected to surpass $18.4 billion by 2034. With more than 200 telecom operators already experimenting with QKD and growing investment in quantum satellite communications, this technology is emerging as a strategic cornerstone of the cybersecurity landscape—one that will define how information is protected in the quantum era.



